In today’s globally connected world, the ability to leverage data leads to better decision-making and competitive advantages. However, using data – whether for analytics, machine learning, or cross-jurisdictional collaboration – often introduces significant organizational risks.
Privacy Enhancing Technologies (PETs) have emerged as a critical solution, allowing organizations to effectively utilize data without compromising privacy and security.
The Core Problem: The "Data in Use" Gap
To understand the value of PETs, it is helpful to start by understanding at The Data Triad, which categorizes data into three states:
- Data at Rest: Data stored in file systems or databases.
- Data in Transit: Data moving through a network.
- Data in Use: Data currently being processed, searched, or analyzed.
While industry standards dictate robust encryption for Data at Rest and in Transit, Data in Use has historically been a vulnerability. When organizations extract value from data by performing basic functions such as searches, analytics, or machine learning, they often expose sensitive content, potentially violating regulatory standards, compromising security boundaries, or exposing intent.
What Are Privacy Enhancing Technologies?
PETs are a family of technologies that protect data while it is being used or processed. By securing the user’s interaction with the data, PETs bridge the Data in Use gap in the data lifecycle, allowing sensitive assets to be securely and privately utilized and value to be unlocked.
Implementing PETs aligns with Zero Trust strategies by focusing on a data-centric approach to data usage, ensuring protection for the data assets themselves rather than just the broader network.
The Three Technology Pillars of PETs
The PETs category is defined by three technology pillars, often used in complementary ways depending on the use case:
- Homomorphic Encryption (HE): This allows data to be processed in its encrypted state (ciphertext) as if it were unencrypted (plaintext). HE ensures that sensitive data is never exposed during processing. Notably, HE is lattice-based, making it quantum resistant and a strong long-term choice against future quantum computing threats.
- Secure Multiparty Computation (SMPC): A protocol that protects data by enabling it to be processed across multiple parties.
- Trusted Execution Environments (TEEs): Also known as Confidential Computing, this is a perimeter-based security technology that exists on the hardware itself.
Strategic Business Value and Use Cases
Adopting PETs allows organizations to solve real-world business problems at scale.
- Secure Collaboration: PETs enable organizations to leverage third-party, commercial, or open-source data assets to unlock value without increasing organizational risk.
- Enabling Secure AI: The implications of PETs for Artificial Intelligence (AI) are critical. PETs allow models to be trained over disparate data sources without compromising the underlying datasets and protects models from attacks like spoofing or poisoning during evaluation.
- Reducing Risk: For banks and other regulated businesses, PETs allow users to extract unique insights via secure search and analytic capabilities while ensuring the protection of sensitive information. This is vital for enabling data usage across silos and jurisdictions and minimizing risk during critical business functions such as customer onboarding and fraud investigations.
Implementation Strategies for Enterprises
There is no one-size-fits-all solution for protecting the usage of data, but organizations generally follow one of three paths when adopting PETs:
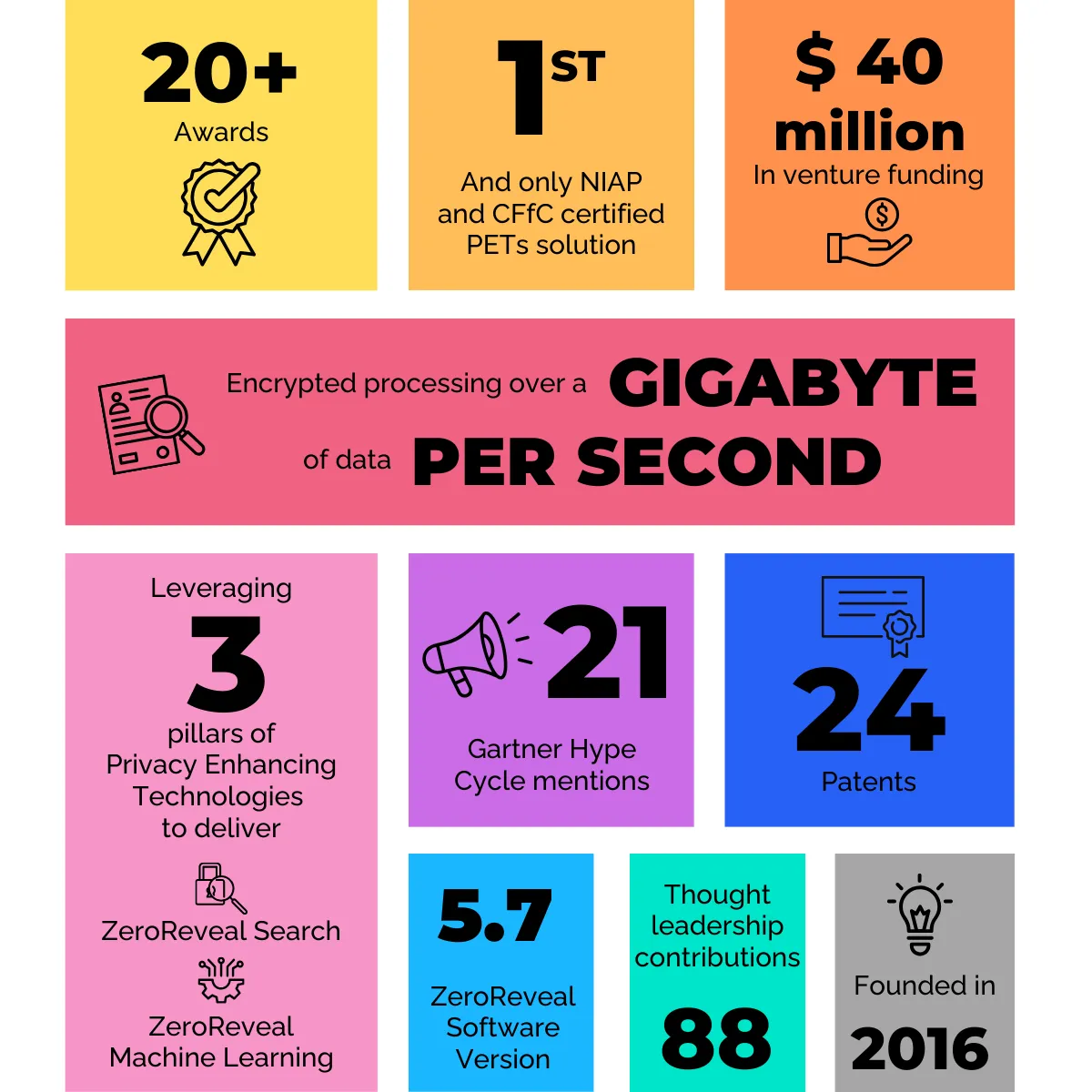
- Leverage Enterprise-Ready Solutions: Utilizing Commercial Off the Shelf (COTS) solutions to efficiently address near-term challenges. Enveil’s PETs-powered ZeroReveal® solutions unlock data value across silos and boundaries, enabling organizations to securely and efficiently leverage data in-place and at scale.
- Build In-House: Organizations with sufficient time and expertise may build solutions using open-source building blocks, though this requires highly specialized skills to ensure the solution is hardened for enterprise use.
- Pursue a Hybrid Approach: Some chose to utilize a mix of COTS solutions, consulting services, and internal tools to craft solutions using PETs.
Conclusion
As market drivers and global policy shifts continue to solidify the need for private and secure data usage, protecting Data in Use is becoming standard practice. By adopting Privacy Enhancing Technologies, organizations can capitalize on expanded data sources while minimizing risk exposure, ensuring they remain ahead in a data-driven era.