What are Privacy Enhancing Technologies and how do you use them?
Privacy Enhancing Technologies, or PETs as they are sometimes called, are a powerful family of technologies that protect Data in Use, enhancing and preserving the security and privacy of data throughout its processing lifecycle. These technologies are transformational because the capabilities they deliver aren’t making current processes, systems, or workflows better; they are making something entirely new possible.
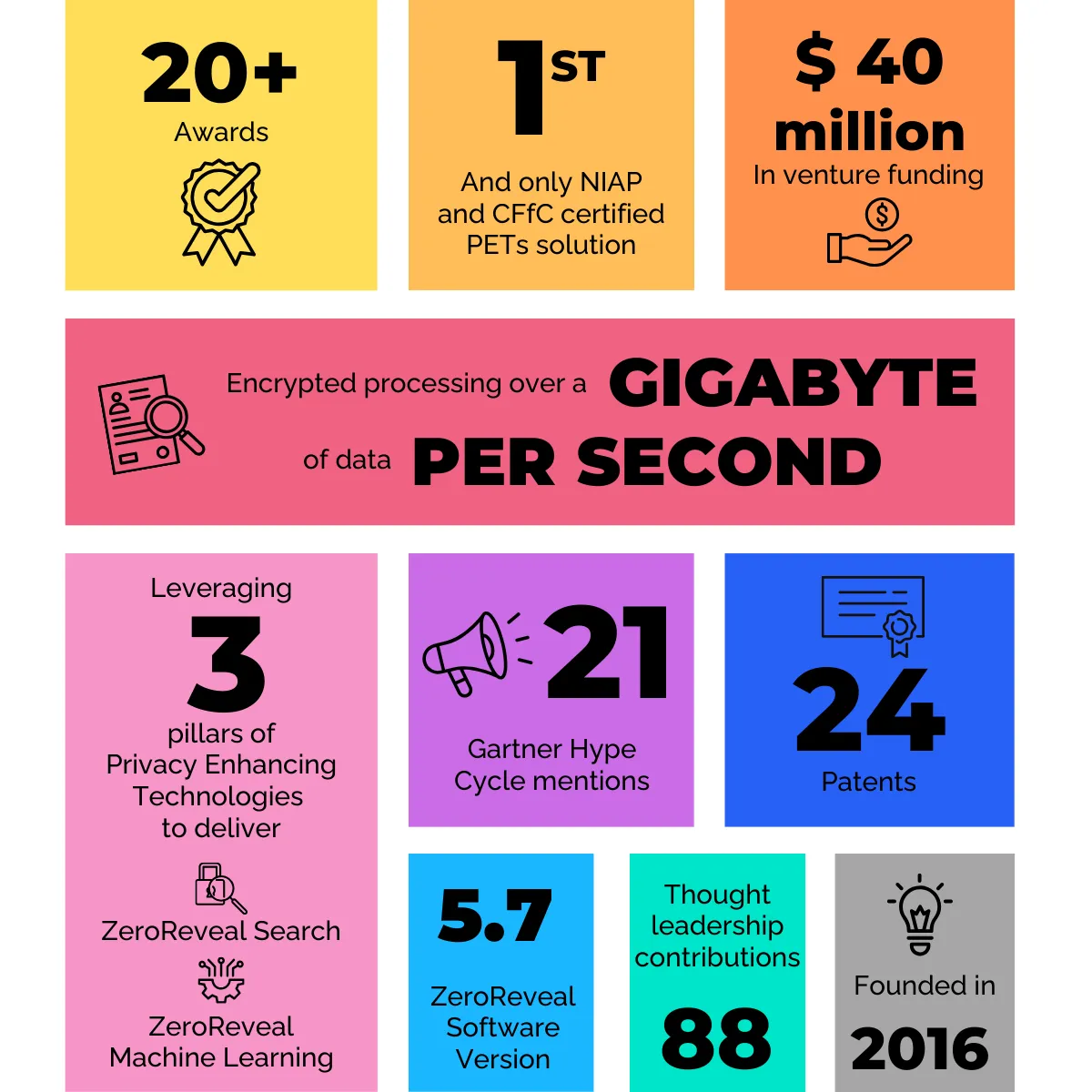
Our ZeroReveal solutions, which leverage several pillars of the PETs category including homomorphic encryption, secure multiparty computation, and trusted execution environments, make PETs practical, scalable, and performant for real business and mission use cases today. Data is the backbone of the digital economy and we enable organizations to utilize it for business purposes while ensuring privacy, security, and regulatory barriers are respected and their interests are protected.
What is homomorphic encryption?
By its most basic definition, homomorphic encryption (HE) secures Data in Use by allowing computations to occur in the encrypted or ciphertext domain. If encryption is a vault protecting sensitive data, traditional practice requires taking that data out of the vault every time it needs to be used or processed (perform a search, apply analytics/machine learning, etc.). This exposure leaves the data and the operation vulnerable. HE allows these actions to take place within the vault, ensuring the interaction and the corresponding results remain protected.
A focus of research for more than four decades for its transformative potential, computational barriers once kept HE relegated to the academic/research arena or some enigmatic government spaces. However, recent and continual breakthroughs have now made it practical for a wide-range of commercial and mission applications, taking HE from exclusive academic darling to commercial game changer. HE is often hailed as the 'holy grail' of cryptography for its paradigm-shifting potential to revolutionize how and where organizations can securely and privately leverage data assets. We are proud to bring that credence to life.
Do you sell proprietary cryptography?
No – and if a company is trying to sell you proprietary crypto, we suggest you run in the other direction.
Our breakthroughs are in the utilization of homomorphic encryption and other Privacy Enhancing Technologies. We leverage core HE building blocks, which allow you to either add or multiply in ciphertext, and use them to create products that address real business and mission problems. Our solutions enable users to encrypt a search, analytic, or machine learning model and perform the operations without ever decrypting the content of the search or its corresponding results.
Our products can leverage any type of HE – that can, and often does, include open source HE libraries such as Microsoft SEAL.
I’ve read academic research on homomorphic encryption – are you a research firm or an HE library?
Neither actually. We build solutions that creatively and efficiently leverage homomorphic encryption and other Privacy Enhancing Technologies to solve real business and mission problems. In contrast, HE research is focused on advancing the core mathematical HE cryptographic components. We applaud those doing HE research, and view their work as complementary to our work at Enveil.
There is a significant difference between an HE library and an HE-powered solution. You can think of an HE solution as the house, while an HE library is one of the raw materials, like brick or lumber. HE libraries provide the basic cryptographic components for enabling the capabilities and are often created and maintained by HE researchers, but it takes a lot of additional work, including software engineering, innovative algorithms, and enterprise integration features, to get a usable, commercial grade product. Vendors providing HE solutions have already built the house, often leveraging various HE libraries, so while some remodeling may be required to ensure that the solution addresses specific needs, the heavy lifting is done.
Are PETs performant enough for commercial use?
Yes — in fact, commercial and government entities are using Privacy Enhancing Technologies (PETs) operationally at scale today to solve real problems. While some PETs, namely homomorphic encryption, were once considered too slow to be practical for commercial use at scale, that is no longer the case. Advances in the underlying HE technology, as well as efficiencies relating to its use that we have pioneered, mean that HE can now operate at the speed of business for a number of use cases, alongside other PETs. Encrypted searches can be performed over hundreds of millions of data records and returned within seconds rather than days or even weeks (yes, it started out that slow).
How do your solutions advance operational efficiency?
Enveil's innovative COTS capabilities allow users to stop moving data and start using it — securely. This enables operational efficiencies by substantially reducing costs and delivering unprecedented speed to insights. By encrypting sensitive searches, watchlists, and ML models that run over cross-silo data, Enveil’s software utilizes PETs to eliminate the need to move or replicate large datasets or infrastructure in order to extract value. This encrypted data usage enables secure cross-boundary data collaboration, allowing organizations to utilize disparate datasets in a manner that is secure, efficient, and provides operationally-relevant insights. Enveil’s capabilities are deployed today, streamlining data usage by reducing duplication of effort, data, and infrastructure while expanding the full array of sources available to decision makers.
Does your solution protect all my data, all the time?
No, we exclusively focus on protecting data while it's being used or processed, also known as Data in Use. This is different from other common forms of encryption, such as those that protect Data at Rest on the file system, or Data in Transit as it moves through the network. You can think of Data in Use as the interaction with the data – we encrypt the search, analytic, or machine learning model itself, as well as the corresponding results, and ensure it stays encrypted throughout the processing lifecycle. Using Enveil, organizations can securely derive insights, cross-match, and search third-party data assets without ever revealing the contents of the search itself, compromising the security or ownership of the underlying data, or exposing their own interest in the data.
Do I need to pool or centralize my data in order to use ZeroReveal?
No, we specifically designed our software to support a decentralized approach to data sharing and collaboration since we know that requirements to move or pool sensitive assets are often deal breakers for our customers. Enveil ZeroReveal allows all participating organizations to retain positive control and ownership of their sensitive data assets at all times. We will never ask you to move data to a centralized data lake or repository, an approach that differentiates us from many of our competitors. We enable customers to perform encrypted processing over data where it is and as it is today.
Enveil delivers secure and efficient data usage at scale by allowing datasets to be used in-place across silos and security boundaries, including multi-domain, multi-jurisdiction, and third-party environments, eliminating the need to replicate data into higher-trust systems for processing. This creates workflow efficiencies that deliver immediate cost-savings via reduced resources for data ingest, compute, and storage.
How does ZeroReveal help customers address regulatory challenges?
In an increasingly regulated ecosystem, data sharing limitations often impede critical business functions and restrict data sharing and collaboration across jurisdictions, internal silos, and organizational boundaries. By never decrypting searches, watchlists, or analytics during processing, Enveil ZeroReveal allows entities to securely and privately share and collaborate while retaining positive control of their data assets. This collaboration can occur in a secure, decentralized manner while protecting organizations against the risk of data breaches, regulatory penalties or brand and reputational damage.
Do I need to re-encrypt my data in order to use ZeroReveal?
Nope. Enveil is built to enable encrypted processing over data wherever it sits – in the Cloud, on Prem, or in a third-party data environment. Our software sits above the data, allowing organizations to maintain control of their data assets while leveraging existing storage methods, access, and audit controls. Enveil ZeroReveal is a lightweight, proxy-layer software system designed to work at the speed of business within existing customer workflows. The deployment model is optimized for highly distributed, decentralized multi-party, or hybrid cloud deployments.
How is ZeroReveal used in the federal space?
Most of our
federal work centers around enabling users to perform trusted compute in what they consider to be untrusted locations. By keeping search terms, analytics, and machine learning models encrypted during processing, Enveil allows operators and analysts to securely derive insights, cross-match, and search untrusted data assets. This can be done across multiple data sources – even when using sensitive or classified indicators. Enveil protects not only the content of the interaction, but also the interests, intent, and TTPs of the party performing the search or analysis. This allows data to be leveraged in ways that were never before possible for use cases such as secure cross-domain data usage and tactical edge collaboration.
Are your solutions quantum resistant?
Yes, the homomorphic encryption (HE) leveraged by Enveil ZeroReveal is quantum resistant. The strength of HE comes from lattice-based encryption techniques, which are not vulnerable to known quantum algorithms and have been designated by NIST as quantum resistant. Customers can be confident in the security of ZeroReveal as well as the software’s ability to adapt to future guidance from standard bodies. The modularity of our software allows us to "plug in" customer-preferred cryptography modules, ensuring that we are able to maintain pace with future post-crypto algorithm development.