- The ability to share sensitive information securely is a defining feature of the cybersecurity community.
- Privacy-enhancing technologies (PETs) are emerging as a key way to overcome the challenges involved in sharing data.
- Implementing these technologies will usher in a necessary - and urgent - paradigm shift.
Cybersecurity is one of the most systemically important issues facing the world today. In little over a decade, cybersecurity has been transformed from a principally technical domain centred on securing networks and technology to a major strategic topic of global importance. Cybersecurity is a pillar of a digitally resilient society, but its community is now facing the challenges that come with the rapid pace of the technical, regulatory, and broader systemic changes that are happening at a global scale.
Intelligence sharing between stakeholders is a defining feature of the cybersecurity community and one of its most important shared challenges. No stakeholder alone can sustainably identify and address all of the cyber-threats of the fast-changing digital landscape. The World Economic Forum has recently published a report that identifies seven major barriers to cyber information sharing that need to be addressed to help build collective security – from addressing an increasingly complex regulatory landscape, to issues over trust and privacy, and organizations having access to the right tools, capabilities and skills.
Cybersecurity is not the only industry pursuing ways to facilitate better information sharing and more effective collaboration – the same pressures are emerging in other verticals including healthcare and financial services. Technology offers solutions to these challenges. Much of the technical and policy community focus is on artificial intelligence (AI) and machine learning as solutions, but privacy-enhancing technologies that enable sharing while protecting privacy and security are now becoming more accessible and understood, and offer significant opportunities for both information-sharing and wider value propositions to business.
Privacy-enhancing technologies
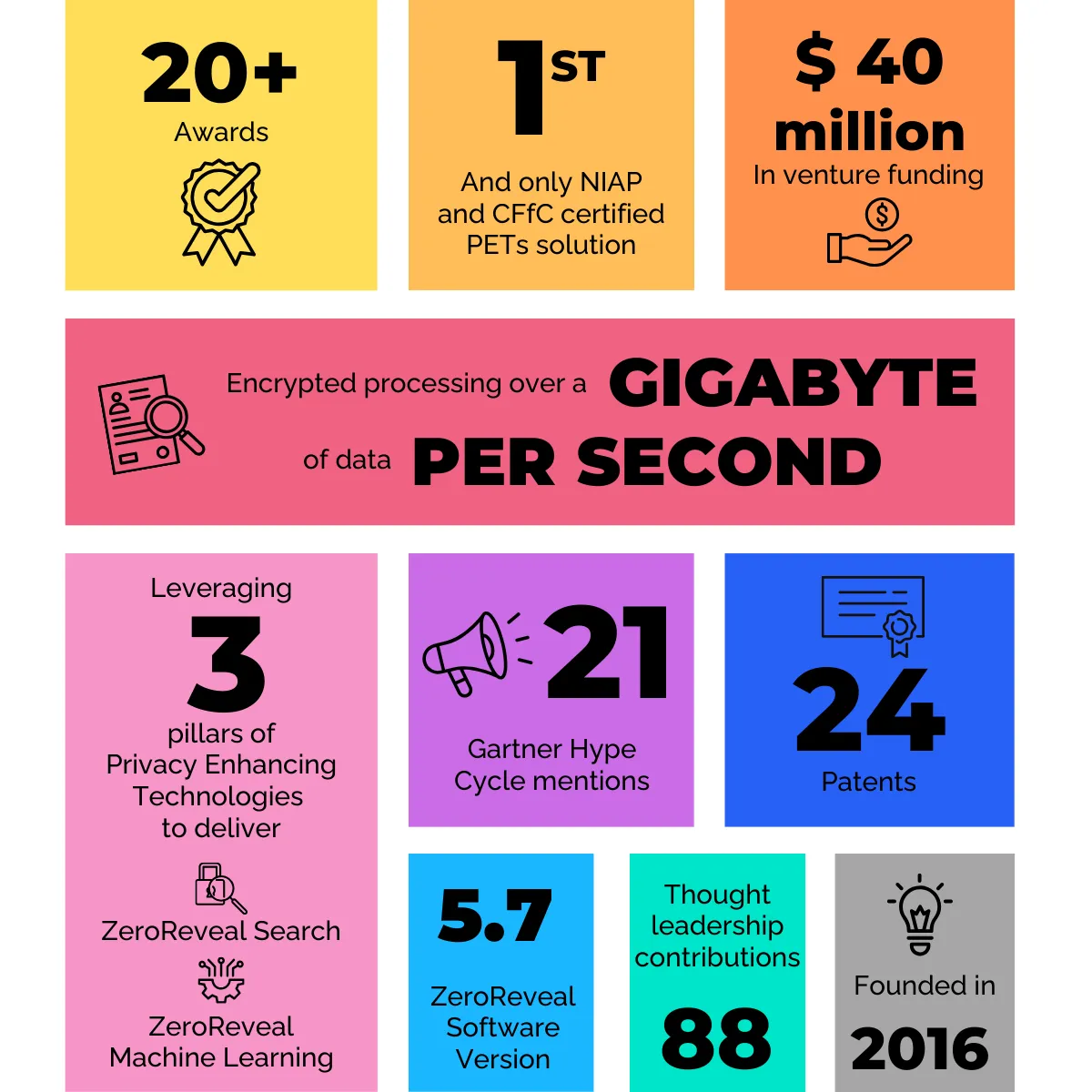
Privacy-enhancing technologies (PETs) are emerging as a key way to overcome the challenges implicit in the need to deliver a better information-sharing paradigm. They can deliver increased cyber resilience between organizations and help drive collective action against cybercriminals through deeper partnerships between the private sector and governmental bodies.
Privacy Enhancing Technologies (PETs) enable sharing while protecting privacy and security.
Potentially transformative thanks to recent advances in both development and availability, PETs can provide assurances to senior leaders that the benefits of data sharing can be realized while adhering to data protection and privacy requirements, and while managing corporate risk by "enabling the analysis and the sharing of insights without requiring the sharing of the underlying data itself”. This overcomes one of the principal barriers to current information-sharing models.
These technologies will grow in importance for the future of information sharing because they can overcome any lack of trust as well as satisfying privacy regulations and legal mandates. These requirements demand that systems have safeguards in place to protect against malicious attempts to access or derive sensitive data from within them. Focus on these technologies is currently centered on case studies in compliance-heavy industries such as financial services or healthcare, but they are also potentially transformative for collective cyber investigations because of three emerging capabilities that PETs enable:
1. Secure and federated data analysis: organizations can have their encrypted data analysed by AI and analysts without revealing the underlying data.
2. Secure data linkage: multiple organizations can contribute encrypted data for joint decentralized analysis and investigations.
3. Secure search: organizations can send encrypted queries to one another’s databases without revealing the details of their query.
For the cybersecurity and financial crime community, this is significant for enabling joint investigations between the public and private sectors, which can drive collective action. These technologies could be used to identify potential data and investigative opportunities in different organizations and jurisdictions with high levels of assurance and integrity without sharing the data with each other directly.
More work is required to identify new pilots to assess applicability in facilitating more effective joint investigations for cybersecurity and cybercrime use cases. Regulators and government bodies, especially those with oversight of cybersecurity investigations, need to issue guidance on the applications, use and deployment of PETs to accelerate their adoption.
More widely, this ability to process encrypted queries over third-party datasets advances information sharing and collaboration to deliver business value. For private companies, the ability to secure shared data across jurisdictions or silos within their own organization as well as with work collaboratively on sensitive data with third‐parties opens the door to a number of business use cases that are currently restricted or prevented by regulatory and legal barriers.
Technologies can build information sharing 2.0
The need for information sharing 2.0 is rooted in the acknowledgment that there is a clear need to adapt sharing to fit this new world, one in which collaborative efforts ensure the security and privacy of sensitive global data assets. This requirement is even more evident in our current tumultuous global climate, which has seen a dramatic increase in cybersecurity threats, financial crime and challenges associated with the COVID-19 crisis.
The solution is not simple. It will require a concerted, coordinated effort by regulatory bodies as well as leaders in the public and private sector. But advances in PETs are providing us with the tools we need to rethink the way we share information. Continued efforts to propel the category’s visibility and adoption is key to driving sustainable change, because the shift to information sharing 2.0 is not a better way of doing what we’ve always done. It marks a paradigm-shifting advance that can change the way we interact by enabling collaboration that prioritizes the security and privacy of data assets.