The world is undeniably interconnected and, working together, we advance farther faster — a sentiment that frequently holds true in the business world as well. Organizations are always working to identify and make use of every possible advantage, and collaboration has emerged as a path to accelerating advances and increasing efficiency. As data is the backbone of the digital economy, it is not surprising that the shared utilization of data resources often spurs such efforts. Data sharing and collaboration allow businesses to extract insights from collective purchasing trends to predict buyer behavior; monitor disparate interactions across a multiparty supply chain; or cross-reference customer lists and transactions to identify patterns that may signal nefarious or fraudulent activity.
Consider a bank interested in increasing its efforts to combat money laundering, a problem that consumes roughly three percent of the global GDP each year. During customer onboarding, banks perform due diligence to gain an understanding of the person seeking to open an account, and then evaluate that potential customer based on a risk rating score derived from the information gathered. These evaluations frequently fail to paint the whole picture, in part because the bank is limited to the information available within their own country or jurisdiction. Regulations created to serve an important role in protecting customer privacy often prevent banks from sharing data, even with branches of their own organizations. Criminals understand these limitations and take advantage of them by opening accounts in multiple jurisdictions. But what if the onboarding bank could efficiently collaborate with these other branches — or even with other banks or public entities like law enforcement? Such sharing and collaboration would provide a much clearer picture of the potential customer and allow the bank to make better, intelligence-led decisions prior to opening accounts.
So why aren’t we collaborating this way today? Why can’t banks pool their data resources in a consolidated, centralized database to identify and remove these criminals from the global financial system? Because despite the value delivered, organizations know that the benefits gained frequently do not outweigh the risks introduced.
There are numerous reasons why the seemingly simple concept of a centralized data sharing approach is infeasible — violating customer privacy, disregarding data localization requirements, revealing potentially competitive information, and creating single points of security failure are only a few of the issues. Moreover, organizations are unwilling to increase their own risk and liability by giving up positive control of their data assets, even when it might be done to prevent criminal activity. Any requirement to pool or move data to a central location is often a nonstarter as there is no value add that is worth violating privacy restrictions and/or compromising customer trust. Cisco’s 2020 Consumer Privacy Study concluded that “people care deeply about protecting their data, and many have stopped doing business with companies due to data privacy concerns.”
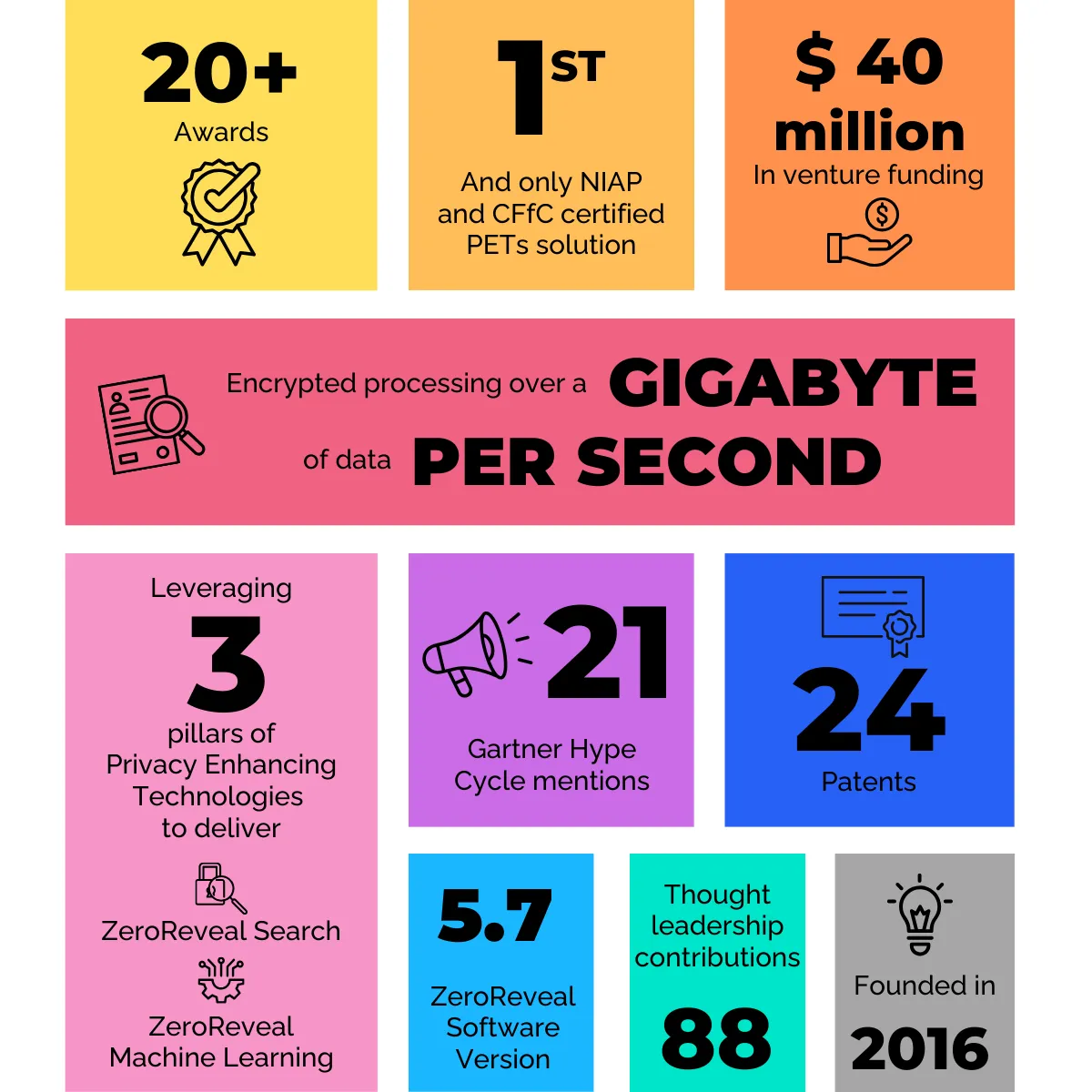
This unwillingness and practical inability to pool or centralize data does not mean there is no way to overcome these challenges and effectively collaborate — it just means we need to find a better path. Enter homomorphic encryption, a pillar of an important and increasingly visible category known as Privacy Enhancing Technologies (PETs). Broadly speaking, PETs enable and strengthen the private and secure usage of sensitive assets by protecting data while it’s being used or processed, uniquely allowing organizations to share and collaborate while ensuring sensitive data remains protected.
For example, when homomorphic encryption (HE) is used to specifically protect the interaction with the data (such as the query or analytic itself), collaboration can take place in a decentralized manner that allows all contributors to maintain positive control and ownership of their data assets. Since HE uniquely enables encrypted processing, it protects the content of the query without exposing sensitive information to any other collaborator. It also allows the data to be used as it is and where it is today, a critical feature since potential collaborators rarely (if ever) have infrastructures or data formats that look exactly alike. By leveraging HE, third-party entities — or users in different privacy jurisdictions or divisions of the same organization — can securely and privately work together in ways that were never before possible. The technology opens the door to opportunities for collaboration across private industry and between public and private entities.
To paint a picture of what this type of HE-powered decentralized collaboration might look like, consider the previous example outlining a global bank’s customer onboarding process. Using HE, the bank could encrypt a search in the jurisdiction where the customer is trying to open an account and send that encrypted search to run against customer databases in other jurisdictions. Once the search is performed without ever exposing the customer information, the encrypted result is returned to the onboarding jurisdiction and only then is the information decrypted and viewable to the analyst. Because HE allowed that search to be processed while encrypted, customer privacy is maintained and regulations are respected, giving the bank a broader and clearer picture of the customer without introducing additional risk.
Beyond financial services, there are many ways HE-powered, decentralized collaboration could enable business functions across verticals: supporting sensitive data sharing in the healthcare industry for efforts like vaccine development, facilitating a data marketplace where partners could contribute to and access consumer transaction records in a secure and private way, allowing industry groups to benchmark trends without exposing individual contributors, and enabling manufacturers to monitor equipment performance statistics without compromising customer usage patterns. And thanks to recent breakthroughs in the utilization of HE, all of this can happen in a matter of seconds.
Read the full article on ITProPortal.