Revenue is the lifeblood of any business, and finding new, untapped revenue streams is the stuff CEO dreams are made of. Organizations are increasingly recognizing that responsibly monetizing data assets can provide new revenue opportunities, even spurring the creation of entirely new products and business lines.
If organizations want to securely and ethically monetize data resources, they must do so in a manner that respects the privacy of both the customers using the new monetization service and the underlying data itself. This requires organizations to fully define and understand what it means to securely use data. This process of discovery is increasingly leading to the adoption of a data-centric approach to security.
A data-centric approach to security means focusing on the security of the data itself — rather than the networks, architectures or perimeters it is located within — and it is imperative in the reality of our zero-trust operating environments. An effective data-centric security strategy protects data throughout its life cycle, whether sensitive assets are at rest (on the file system), in transit (moving through the network) or in use (actively being used or processed). These elements can be visualized as forming the three components of the Data Security Triad.
A data-centric security model enables secure data monetization as it provides organizations with the flexibility they need to remain compliant in today’s ever-changing regulatory environment. Data-centric security also fulfills the "security by design" approach required as part of the General Data Protection Regulation (GDPR), which has proven to be the leader among global data protection standards since it took effect in May 2018.
This is good business practice not only because it will help avoid the fines dictated by the legislation, but also because it demonstrates that an organization is making a concerted effort to respect consumer privacy, which is critical when it comes to monetizing any data assets.
Gartner predicts that "by 2023, 65% of the world’s population will have its personal information covered under modern privacy regulations, up from 10% today." This affirms that a solid privacy and security strategy must be foundational to any use of data, including monetization. And for those of us operating in the B2B space, a proven date-centric security strategy makes us more appealing as partners, suppliers and collaborators.
So, what technologies enable the data-centric security and privacy we need in order to monetize existing data assets while respecting regulatory and ethical boundaries?
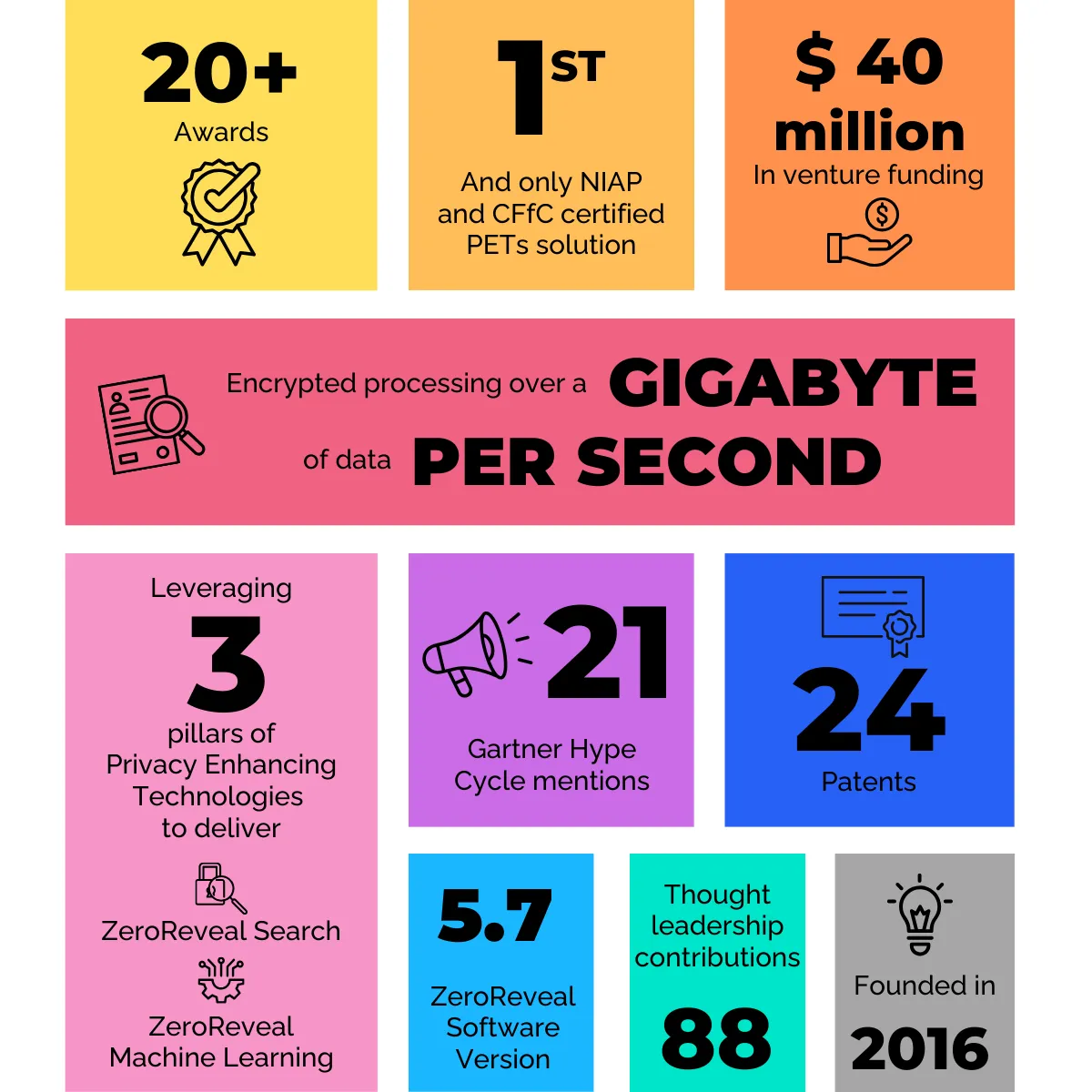
Recent advances in the segment of privacy-preserving — or privacy-enhancing, as it is more commonly referred to in the UK/EU — technologies have made it is possible to ensure that nothing is exposed during the data processing life cycle. The category includes technologies such as homomorphic encryption, secure multiparty computation and secure enclaves, which were previously confined to discussions in academic spaces but have now innovated to the point of commercial readiness. What once was computationally impractical can now be completed in a business-relevant time frame, a key threshold for gaining commercial traction.
Using these capabilities, which allow data to be processed in a privacy-preserving manner without risk of exposure, organizations can now leverage data in ways previously determined to be too risky to pursue.
Here are five questions organizations should ask themselves before moving forward with a data monetization strategy:
1. Are we ensuring all necessary stakeholders within the organizations are on board? While the monetization of data assets is increasingly driven by the office of the CDO, it is important that the security and privacy teams are part of the process as well so risks can be appropriately identified.
2. Are we respecting the privacy and security of data throughout its life cycle? By ensuring data is protected at rest, in transit and in use, we can eliminate vulnerability gaps that lead to breaches and misuse. This is critical — especially if the data is to be shared with a third party.
3. Are we protecting data ownership? When it comes to data monetization, one of the biggest nonstarters is typically the need to combine or move data assets to a third-party location. There are a number of issues with this approach, only some of which involve data privacy. But privacy-preserving technologies overcome that challenge by enabling a decentralized framework for secure data sharing and collaboration as well as integrating with existing access control measures.
4. Do we have a plan or governance framework to address changes in regulations, third-party relationships, etc.? Regulations will change over time. Any data monetization approach must be flexible enough to adapt to these changes or else the system will quickly become a waste of time and resources.
5. Can I audit the outcomes without exposing the data? Any system involving third parties must have an audit trail. But if the audit system exposes everything you have worked so hard to protect, it defeats the purpose of your efforts.
There are new revenue opportunities waiting to be unlocked by securely monetizing existing data assets in a privacy-preserving manner. However, while pursuing technical answers to the question of "Can we?" organizations must also consider the foundational questions of "Should we?" before they embark. Data monetization should only be pursued in a way that fully respects the privacy and security of the data. Privacy-preserving technologies can deliver on that commitment, providing organizations with a path to ethically leverage data assets.
Read the full article at Forbes.