Data is the backbone of the digital economy. It can inform our decision making, increase our efficiency, and shape our behaviours. So naturally, most businesses are on a constant quest for better data — and much more of it.
When we hear the term data sharing and collaboration, our first inclination may be to assume that it’s referencing the actual movement of data from one location to another.
And while there are certainly circumstances where that needs to happen, let’s consider data sharing in the context of data usage. (We’ll leave the Privacy Shield and related discussions for another day.) Because the heart of many business ‘data sharing and collaboration’ use cases is not the actual movement of data, but rather our ability to use data to extract value.
The critical business need for and value of global information sharing and collaboration has never been greater. It is horizontal across industries, spanning all kinds of use cases and all types of data.
Simultaneously, there is an unprecedented demand for global privacy and an ever increasing heterogenous regulatory landscape. We know that moving or replicating large amounts of data, whether between organisations or across internal silos, can be complicated and risky, if not practically impossible, especially if any of that data is sensitive.
So how can organisations overcome these internal and external information sharing barriers to focus instead on secure and private data usage for value creation?
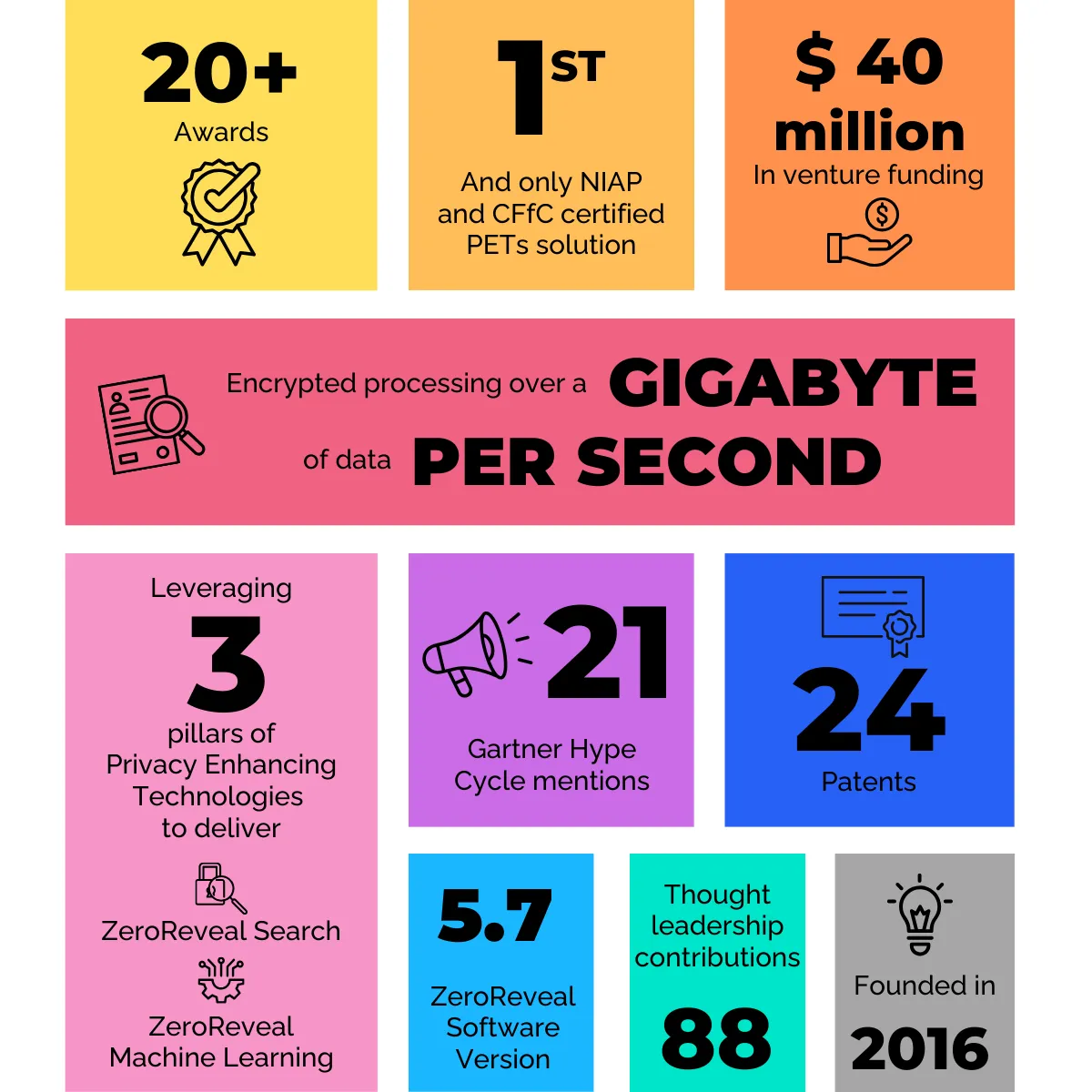
On the forefront of this shift is the accelerating innovation happening in the category of Privacy Enhancing Technologies. Also sometimes referred to as privacy-enhancing computation, this group of business-enabling and privacy-preserving technologies protect data during processing, allowing sensitive assets to be shared and analysed without compromising security or inhibiting use.
Homomorphic encryption, differential privacy, secure multiparty compute, and trusted execution environments are all Privacy Enhancing Technologies (PETs) being used today to enhance privacy and facilitate secure information sharing.
While PETs are not new — they have been researched and used for niche applications in the academic, government, and commercial spaces for more than three decades — the category has gained visibility recently thanks to the growing prioritisation of privacy on a global scale as well as advances that have made the technologies computationally practical for broad commercial use.
Just this week, Gartner named privacy-enhancing computation as one of its 2022 Top Strategic Technology Trends and estimates that 60% of large enterprises will be leveraging one or more of these techniques by 2025.
To highlight a practical business use case for PETs-enabled data sharing, let’s examine how the technology can be applied to a common information sharing challenge in the financial services sector.
This onboarding/Know Your Customer use case was the focus of a TechSprint hosted by the Financial Conduct Authority and is a scenario global banks encounter on a daily basis. Imagine a prospective customer wants to open a bank account and therefore provides the bank with basic identifying information (name, address, occupation, etc.).
The bank uses this information to search its system for existing account information as well as any red flags that might indicate increased risk associated with this potential new customer. However, despite having access to its own global information network, privacy regulations limit the information the bank can actually search.
This inability to efficiently share or cross-reference information with branches in other jurisdictions leaves the onboarding bank with incomplete information — and, ultimately, a customer risk rating that may not be accurate.
PETs (in this case, homomorphic encryption) changes the game by enabling the bank to widen the aperture of its search while still protecting the customer’s personally identifiable, and therefore regulated, information.
Leveraging homomorphic encryption, the bank is able to encrypt its search within its own trusted environment, send the encrypted search across to other jurisdictions where it can be securely performed over other intra-bank data sources — all while ensuring the sensitive content of the query is never decrypted outside the walls of the onboarding bank.
When the encrypted search results are returned to the requesting party, analysts are able to calculate a more accurate, informed customer risk rating, allowing the bank to make an intelligence-led onboarding decision. And, through the power of PETs, all of this can be done at the speed of business while ensuring the privacy of the prospective customer remains protected.
Similar impact can be seen for data sharing use cases across verticals. In healthcare, PETs allow public and private entities to securely collaborate with sensitive data (think vaccine research) across multiple architectures, repositories, and security domains for medical facilities and mobile testing sites.
Public health officials or healthcare workers in any location could securely query sensitive patient and/or health data no matter where that data may reside — and without the need to move or replicate. For cybersecurity teams, PETs can be used to securely share breach findings to more quickly and efficiently address issues without exposing the specific entity, sensitive data, or other risk-inducing identifiers.
More broadly, Privacy Enhancing Technologies can be used to uncover untapped revenue streams by allowing organisations to securely and ethically monetise data assets without fear of exposure.
At the end of the day, the need to share and collaborate with data to unlock value is a very real challenge faced by a wide-range of businesses. It’s an imperative for full participation in the growing digital economy.
Data owners and users are increasingly acknowledging the existing barriers and looking for innovative solutions to overcome them — and Privacy Enhancing Technologies are delivering solutions. PETs provide new avenues to enable secure data usage while still preserving the privacy and security of sensitive data assets, and in the process, are changing the way we do business.
Read the full article at DIGIT.